Tuesday 29 November 2016
Dharma and Karma: A Tale of Two Ransomwares | www.cioandleader.com
Posted on 03:19:00 by ivajrasecurity with No comments
Thursday 24 November 2016
Posted on 00:44:00 by karthick with No comments
Ransomware Decryption ToolsRansomware is malware that locks your computer or encrypts your files. You can’t get the data back unless you pay a ransom, and even if you do, there’s no guarantee that you’ll get your data back.
Ransomware Decryption Tools – an ongoing list
Ransomware Decryption Tools – an ongoing list
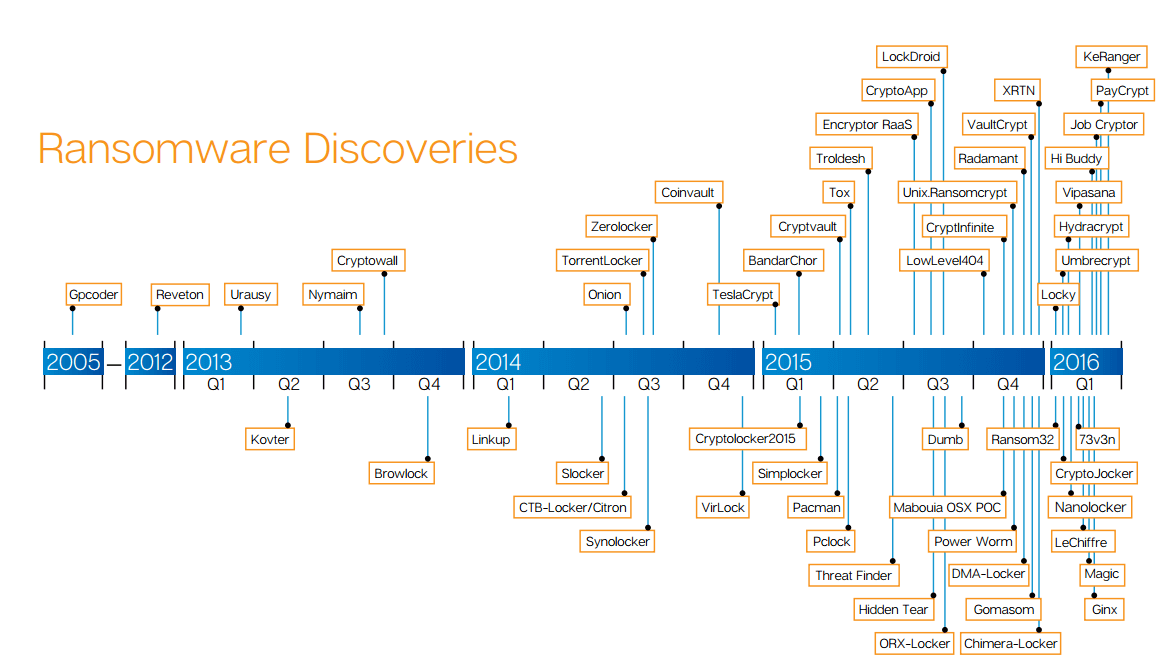
The following statistics would explain the type of Ransomware that emerged since 2005.
Due to emerging of sophisticated Ramsonwares in the Internet, there are no finite solution or decryption tools available in the Cyber security market.
Here we provide a list collected from various sources which will help decrypt the infected files.
we also suggest to take regular backup of critical data in the organisation.
https://decrypter.emsisoft.com/777
https://github.com/hasherezade/malware_analysis/tree/master/7ev3n
https://download.bleepingcomputer.com/demonslay335/hidden-tear-bruteforcer.zip
http://www.bleepingcomputer.com/forums/t/614025/8lock8-help-support-topic-8lock8-read-ittxt/
http://www.bleepingcomputer.com/forums/t/614025/8lock8-help-support-topic-8lock8-read-ittxt/
https://github.com/hasherezade/malware_analysis/tree/master/7ev3n
https://www.nomoreransom.org/decryption-tools.html
https://cta-service-cms2.hubspot.com/ctas/v2/public/cs/c/?cta_guid=d4173312-989b-4721-ad00-8308fff353b3&placement_guid=22f2fe97-c748-4d6a-9e1e-ba3fb1060abe&portal_id=326665&redirect_url=APefjpGnqFjmP_xzeUZ1Y55ovglY1y1ch7CgMDLit5GTHcW9N0ztpnIE-ZReqqv8MDj687_4Joou7Cd2rSx8-De8uhFQAD_Len9QpT7Xvu8neW5drkdtTPV7hAaou0osAi2O61dizFXibewmpO60UUCd5OazCGz1V6yT_3UFMgL0x9S1VeOvoL_ucuER8g2H3f1EfbtYBw5QFWeUmrjk-9dGzOGspyn303k9XagBtF3SSX4YWSyuEs03Vq7Fxb04KkyKc4GJx-igK98Qta8iMafUam8ikg8XKPkob0FK6Pe-wRZ0QVWIIkM&hsutk=34612af1cd87864cf7162095872571d1&utm_referrer=https%3A%2F%2Finfo.phishlabs.com%2Fblog%2Falma-ransomware-analysis-of-a-new-ransomware-threat-and-a-decrypter&canon=https%3A%2F%2Finfo.phishlabs.com%2Fblog%2Falma-ransomware-analysis-of-a-new-ransomware-threat-and-a-decrypter&__hstc=61627571.34612af1cd87864cf7162095872571d1.1472135921345.1472140656779.1472593507113.3&__hssc=61627571.1.1472593507113&__hsfp=1114323283
https://decrypter.emsisoft.com/al-namrood
https://download.bleepingcomputer.com/demonslay335/AlphaDecrypter-fp.zip
http://download.bleepingcomputer.com/demonslay335/AlphaDecrypter.zip
https://decrypter.emsisoft.com/apocalypse
https://decrypter.emsisoft.com/apocalypsevm
http://www.avg.com/us-en/ransomware-decryption-tools#apocalypse
http://www.avg.com/us-en/ransomware-decryption-tools#apocalypse
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/autolocky
https://decrypter.emsisoft.com/badblock
http://www.avg.com/us-en/ransomware-decryption-tools#badblock%20+
http://www.avg.com/us-en/ransomware-decryption-tools#badblock%20+
http://www.avg.com/us-en/ransomware-decryption-tools#bart
https://www.nomoreransom.org/decryption-tools.html
https://download.bleepingcomputer.com/demonslay335/BitStakDecrypter.zip
https://blog.malwarebytes.com/cybercrime/2016/08/decrypting-chimera-ransomware/
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/crypboss
https://github.com/pekeinfo/DecryptCrypren
https://blog.fortinet.com/2016/06/17/buggy-russian-ransomware-inadvertently-allows-free-decryption
http://www.avg.com/us-en/ransomware-decryption-tools#crypt888
https://decrypter.emsisoft.com/cryptinfinite
https://decrypter.emsisoft.com/cryptodefense
http://www.bleepingcomputer.com/news/security/cryptohost-decrypted-locks-files-in-a-password-protected-rar-file/
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/forums/t/565020/new-cryptotorlocker2015-ransomware-discovered-and-easily-decrypted/
https://blog.kaspersky.com/cryptxxx-decryption-20/12091/
https://thisissecurity.net/2016/02/26/a-lockpicking-exercise/
https://github.com/aaaddress1/my-Little-Ransomware/tree/master/decryptoTool
http://www.malwareremovalguides.info/decrypt-files-with-decrypt_mblblock-exe-decrypt-protect/
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/dmalocker
https://decrypter.emsisoft.com/dmalocker2
https://decrypter.emsisoft.com/dmalocker2
https://decrypter.emsisoft.com/fabiansomware
https://decrypter.emsisoft.com/fenixlocker
https://www.nomoreransom.org/decryption-tools.html
https://download.bleepingcomputer.com/demonslay335/GhostCryptDecrypter.zip
https://decrypter.emsisoft.com/
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/gomasom
https://decrypter.emsisoft.com/harasom
https://decrypter.emsisoft.com/hydracrypt
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
http://www.bleepingcomputer.com/download/jigsaw-decrypter/
http://www.bleepingcomputer.com/download/jigsaw-decrypter/
http://news.drweb.com/show/?i=9877&lng=en&c=5
https://decrypter.emsisoft.com/keybtc
https://blog.fortinet.com/2016/04/01/kimcilware-ransomware-how-to-decrypt-encrypted-files-and-who-is-behind-it
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/lechiffre
https://decrypter.emsisoft.com/lechiffre
http://www.avg.com/us-en/ransomware-decryption-tools#legion
https://labs.bitdefender.com/2015/11/linux-ransomware-debut-fails-on-predictable-encryption-key/
https://esupport.trendmicro.com/en-us/home/pages/technical-support/1105975.aspx
http://www.bleepingcomputer.com/forums/t/577246/locker-ransomware-support-and-help-topic/page-32#entry3721545
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/news/security/cryptohost-decrypted-locks-files-in-a-password-protected-rar-file/
http://now.avg.com/dont-pay-the-ransom-avg-releases-six-free-decryption-tools-to-retrieve-your-files/
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://github.com/Cyberclues/nanolocker-decryptor
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/nemucod
https://decrypter.emsisoft.com/nemucod
http://download.bleepingcomputer.com/BloodDolly/ODCODCDecoder.zip
http://www.bleepingcomputer.com/forums/t/559220/operation-global-iii-ransomware-not-only-encrypts-but-infects-your-data-as-well/
https://decrypter.emsisoft.com/pclock
http://www.thewindowsclub.com/petya-ransomware-decrypt-tool-password-generator
https://decrypter.emsisoft.com/philadelphia
http://download.bleepingcomputer.com/BloodDolly/JuicyLemonDecoder.zip
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/news/security/pompous-ransomware-dev-gets-defeated-by-backdoor/
https://www.helpnetsecurity.com/2016/07/22/powerware-ransomware-decrypter/
https://decrypter.emsisoft.com/radamant
https://www.nomoreransom.org/decryption-tools.html
https://support.kaspersky.com/viruses/disinfection/8547#block1
https://support.kaspersky.com/viruses/disinfection/4264
https://www.nomoreransom.org/decryption-tools.html
https://securelist.com/blog/research/69481/a-flawed-ransomware-encryptor/
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/stampado
https://decrypter.emsisoft.com/stampado
http://www.avg.com/us-en/ransomware-decryption-tools#szflocker
http://talosintel.com/teslacrypt_tool/
http://www.avg.com/us-en/ransomware-decryption-tools#teslacrypt
http://www.avg.com/us-en/ransomware-decryption-tools#teslacrypt
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/forums/t/547708/torrentlocker-ransomware-cracked-and-decrypter-has-been-made/
http://www.thewindowsclub.com/emsisoft-decrypter-hydracrypt-umbrecrypt-ransomware
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/xorist
https://decrypter.emsisoft.com/xorist
https://github.com/hasherezade/malware_analysis/tree/master/7ev3n
https://download.bleepingcomputer.com/demonslay335/hidden-tear-bruteforcer.zip
http://www.bleepingcomputer.com/forums/t/614025/8lock8-help-support-topic-8lock8-read-ittxt/
http://www.bleepingcomputer.com/forums/t/614025/8lock8-help-support-topic-8lock8-read-ittxt/
https://github.com/hasherezade/malware_analysis/tree/master/7ev3n
https://www.nomoreransom.org/decryption-tools.html
https://cta-service-cms2.hubspot.com/ctas/v2/public/cs/c/?cta_guid=d4173312-989b-4721-ad00-8308fff353b3&placement_guid=22f2fe97-c748-4d6a-9e1e-ba3fb1060abe&portal_id=326665&redirect_url=APefjpGnqFjmP_xzeUZ1Y55ovglY1y1ch7CgMDLit5GTHcW9N0ztpnIE-ZReqqv8MDj687_4Joou7Cd2rSx8-De8uhFQAD_Len9QpT7Xvu8neW5drkdtTPV7hAaou0osAi2O61dizFXibewmpO60UUCd5OazCGz1V6yT_3UFMgL0x9S1VeOvoL_ucuER8g2H3f1EfbtYBw5QFWeUmrjk-9dGzOGspyn303k9XagBtF3SSX4YWSyuEs03Vq7Fxb04KkyKc4GJx-igK98Qta8iMafUam8ikg8XKPkob0FK6Pe-wRZ0QVWIIkM&hsutk=34612af1cd87864cf7162095872571d1&utm_referrer=https%3A%2F%2Finfo.phishlabs.com%2Fblog%2Falma-ransomware-analysis-of-a-new-ransomware-threat-and-a-decrypter&canon=https%3A%2F%2Finfo.phishlabs.com%2Fblog%2Falma-ransomware-analysis-of-a-new-ransomware-threat-and-a-decrypter&__hstc=61627571.34612af1cd87864cf7162095872571d1.1472135921345.1472140656779.1472593507113.3&__hssc=61627571.1.1472593507113&__hsfp=1114323283
https://decrypter.emsisoft.com/al-namrood
https://download.bleepingcomputer.com/demonslay335/AlphaDecrypter-fp.zip
http://download.bleepingcomputer.com/demonslay335/AlphaDecrypter.zip
https://decrypter.emsisoft.com/apocalypse
https://decrypter.emsisoft.com/apocalypsevm
http://www.avg.com/us-en/ransomware-decryption-tools#apocalypse
http://www.avg.com/us-en/ransomware-decryption-tools#apocalypse
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/autolocky
https://decrypter.emsisoft.com/badblock
http://www.avg.com/us-en/ransomware-decryption-tools#badblock%20+
http://www.avg.com/us-en/ransomware-decryption-tools#badblock%20+
http://www.avg.com/us-en/ransomware-decryption-tools#bart
https://www.nomoreransom.org/decryption-tools.html
https://download.bleepingcomputer.com/demonslay335/BitStakDecrypter.zip
https://blog.malwarebytes.com/cybercrime/2016/08/decrypting-chimera-ransomware/
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/crypboss
https://github.com/pekeinfo/DecryptCrypren
https://blog.fortinet.com/2016/06/17/buggy-russian-ransomware-inadvertently-allows-free-decryption
http://www.avg.com/us-en/ransomware-decryption-tools#crypt888
https://decrypter.emsisoft.com/cryptinfinite
https://decrypter.emsisoft.com/cryptodefense
http://www.bleepingcomputer.com/news/security/cryptohost-decrypted-locks-files-in-a-password-protected-rar-file/
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/forums/t/565020/new-cryptotorlocker2015-ransomware-discovered-and-easily-decrypted/
https://blog.kaspersky.com/cryptxxx-decryption-20/12091/
https://thisissecurity.net/2016/02/26/a-lockpicking-exercise/
https://github.com/aaaddress1/my-Little-Ransomware/tree/master/decryptoTool
http://www.malwareremovalguides.info/decrypt-files-with-decrypt_mblblock-exe-decrypt-protect/
https://www.nomoreransom.org/decryption-tools.html
https://decrypter.emsisoft.com/dmalocker
https://decrypter.emsisoft.com/dmalocker2
https://decrypter.emsisoft.com/dmalocker2
https://decrypter.emsisoft.com/fabiansomware
https://decrypter.emsisoft.com/fenixlocker
https://www.nomoreransom.org/decryption-tools.html
https://download.bleepingcomputer.com/demonslay335/GhostCryptDecrypter.zip
https://decrypter.emsisoft.com/
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/gomasom
https://decrypter.emsisoft.com/harasom
https://decrypter.emsisoft.com/hydracrypt
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
http://www.bleepingcomputer.com/download/jigsaw-decrypter/
http://www.bleepingcomputer.com/download/jigsaw-decrypter/
http://news.drweb.com/show/?i=9877&lng=en&c=5
https://decrypter.emsisoft.com/keybtc
https://blog.fortinet.com/2016/04/01/kimcilware-ransomware-how-to-decrypt-encrypted-files-and-who-is-behind-it
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/lechiffre
https://decrypter.emsisoft.com/lechiffre
http://www.avg.com/us-en/ransomware-decryption-tools#legion
https://labs.bitdefender.com/2015/11/linux-ransomware-debut-fails-on-predictable-encryption-key/
https://esupport.trendmicro.com/en-us/home/pages/technical-support/1105975.aspx
http://www.bleepingcomputer.com/forums/t/577246/locker-ransomware-support-and-help-topic/page-32#entry3721545
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/news/security/cryptohost-decrypted-locks-files-in-a-password-protected-rar-file/
http://now.avg.com/dont-pay-the-ransom-avg-releases-six-free-decryption-tools-to-retrieve-your-files/
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://github.com/Cyberclues/nanolocker-decryptor
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/nemucod
https://decrypter.emsisoft.com/nemucod
http://download.bleepingcomputer.com/BloodDolly/ODCODCDecoder.zip
http://www.bleepingcomputer.com/forums/t/559220/operation-global-iii-ransomware-not-only-encrypts-but-infects-your-data-as-well/
https://decrypter.emsisoft.com/pclock
http://www.thewindowsclub.com/petya-ransomware-decrypt-tool-password-generator
https://decrypter.emsisoft.com/philadelphia
http://download.bleepingcomputer.com/BloodDolly/JuicyLemonDecoder.zip
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/news/security/pompous-ransomware-dev-gets-defeated-by-backdoor/
https://www.helpnetsecurity.com/2016/07/22/powerware-ransomware-decrypter/
https://decrypter.emsisoft.com/radamant
https://www.nomoreransom.org/decryption-tools.html
https://support.kaspersky.com/viruses/disinfection/8547#block1
https://support.kaspersky.com/viruses/disinfection/4264
https://www.nomoreransom.org/decryption-tools.html
https://securelist.com/blog/research/69481/a-flawed-ransomware-encryptor/
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/stampado
https://decrypter.emsisoft.com/stampado
http://www.avg.com/us-en/ransomware-decryption-tools#szflocker
http://talosintel.com/teslacrypt_tool/
http://www.avg.com/us-en/ransomware-decryption-tools#teslacrypt
http://www.avg.com/us-en/ransomware-decryption-tools#teslacrypt
https://www.nomoreransom.org/decryption-tools.html
https://www.nomoreransom.org/decryption-tools.html
http://www.bleepingcomputer.com/forums/t/547708/torrentlocker-ransomware-cracked-and-decrypter-has-been-made/
http://www.thewindowsclub.com/emsisoft-decrypter-hydracrypt-umbrecrypt-ransomware
https://www.nomoreransom.org/decryption-tools.html
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://success.trendmicro.com/portal_kb_articledetail?solutionid=1114221
https://decrypter.emsisoft.com/xorist
https://decrypter.emsisoft.com/xorist
Even if cyber criminals do manage to infect your PC, you can just wipe the system clean and restore your latest backup. No money lost and, most importantly, no important information compromised! So, please, please back up your data. Not tomorrow, not this weekend, not next week. Do it today!
As new types of ransomware emerge, researchers decrypt some strains and others get new variants. There are tens or hundreds of them.
please think about sharing the simple principle of proactive protection with your friends and family. It could spare them the negative experience of being a cyber attack victim.
Wednesday 23 November 2016
Ransomware prevention best practices - OSCE and WFBS
Posted on 05:17:00 by ivajrasecurity with No comments
ɢoogle.com And Google.com Aren’t Same — Stay Away From The Fake Google
Posted on 02:44:00 by ivajrasecurity with No comments
As fishy as it sounds, so true that it exists. The most used google search engine has been the target of spammers to spam user computers. Beware!!!
ɢoogle.com And Google.com Aren’t Same — Stay Away From The Fake Google: Spammers are using a fake Google domain to trick you.
ɢoogle.com And Google.com Aren’t Same — Stay Away From The Fake Google: Spammers are using a fake Google domain to trick you.
Subscribe to:
Posts (Atom)
My Blog List
-
New Microsoft identity and data security capabilities to accelerate CMMC compliance for the Defense Industrial Base - Microsoft introduces new capabilities in Microsoft Entra ID and Microsoft Purview that support CMMC compliance while also helping Defense Industrial Base...9 months ago
-
Data Mining, Sandbox, Malware Classifier & Adversary Emulation - Data driven analysis to achieve any business or strategic goal, also commonly referred as Data Mining, is like finding a needle in a haystack. But when the...5 years ago
-
BIOS Boots What? Finding Evil in Boot Code at Scale! - The second issue is that reverse engineering all boot records is impractical. Given the job of determining if a single system is infected with a bootkit,...5 years ago
-
DellEMC Release of VMware vSphere 6.7 - This blog post is written by Vijay Kumar from Hypervisor Engg. Dell EMC VMware vSphere 6.7 is the next major release after the update release vSphere 6.5 U...5 years ago
-
The Culture Code of a Veteran - *Results, **Winning together, **Integrity, **Customers, and **Innovation.* Five statements that embody Dell’s Culture Code. Interestingly, they also ali...7 years ago
-